Context
Guide centralized open-source component research and surfaced security intelligence at the moment of selection, combining public ecosystem data with Sonatype's proprietary risk insights inside a unified web interface and MCP server.
FEATURED
Designing a developer-facing security intelligence platform that shifts open-source security from reactive enforcement to proactive, confident component selection.
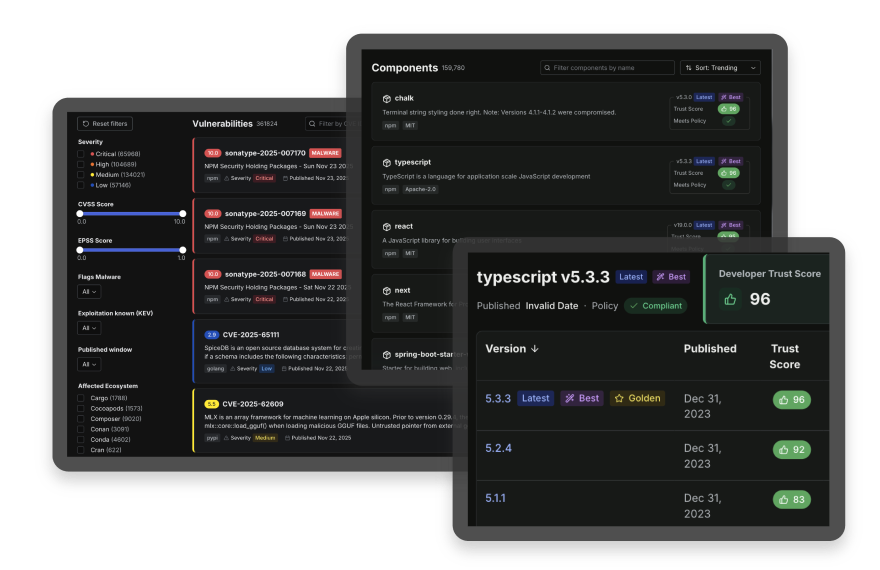
Guide centralized open-source component research and surfaced security intelligence at the moment of selection, combining public ecosystem data with Sonatype's proprietary risk insights inside a unified web interface and MCP server.
As Senior Product Designer, I led end-to-end product design across problem framing, interaction architecture, and scalable system patterns in close partnership with product and engineering leadership.
Developers were forced to interpret vulnerability severity, policy enforcement logic, and component health signals only after enforcement events, often across disconnected systems.
Make high-stakes security decisions easier by clarifying rule hierarchy, surfacing remediation paths, and improving state visibility across complex workflows.
Delivered a unified decision surface that reduced reactive rework, clarified policy intent, and established a scalable foundation for proactive open-source security decisions.
As enterprise organizations are shifting left, greater responsibility for open-source security falls on development teams. From component selection to risk remediation, developers must make decisions in a complex environment where context is fragmented across systems.
Component research happens in a browser. Enforcement happens in CI. Remediation details live in vulnerability reports. Each system provides part of the picture, but none present the full decision context.
As a result, developers are forced to:
Product definition, monetization strategy, marketing positioning, and engineering execution progressed in parallel, requiring scope discipline and decisions that could support both launch and expansion.
Leadership required the product to be designed directly in code rather than through static mockups. The design process itself had to support live prototyping and production-aligned behavior (see Guide UX Lab).
Guide was built using an established third-party design system rather than Sonatype's internal system. Customizations had to remain minimal, requiring thoughtful adaptation rather than reinvention.
Data-heavy interfaces had to preserve hierarchy, contrast, and legibility across themes and breakpoints. UIs were required to support both light and dark modes and adapt fluidly across viewport sizes.
Monetization infrastructure was a launch requirement. The experience needed to support gated proprietary intelligence, tier differentiation, usage limits, billing workflows, and visible credit tracking from the initial release.
Guide is not a policy engine and does not support custom policy configuration. The interface needed to communicate generalized risk and policy concepts without misleading users about configurability.
The product had to serve students and individual developers as effectively as enterprise security teams. The interface needed to scale across levels of expertise and organizational complexity.
Experiences needed to feel intuitive and accessible for net-new developers and existing Sonatype customers. Patterns and terminology had to bridge familiarity and approachability.
The goal was to shift open-source security from reactive enforcement to proactive decision-making, within a compressed release timeline and a monetized product model. Across each decision, the goal was not to eliminate complexity, but to organize and clarify it.
Security context was surfaced at the browsing stage, making risk signals visible before enforcement events or selection decisions. Developers did not need to trigger enforcement or initiate analysis to understand risk.
The experience prioritized transparency around why a component is risky, how severity is evaluated, and what remediation paths are available. Rule hierarchy and state relationships were treated as first-class UI elements.
Guide had to support individual developers and enterprise teams alike. Information architecture emphasized progressive disclosure, allowing rapid triage while preserving depth for deliberate analysis.
Given the tight timeline and design-in-code method, reusable, system-aligned interaction patterns were crucial. Decisions were made at the model level first, ensuring the interface reflected real data relationships.
Guide was designed as a relational security intelligence system, more than a package lookup tool. Components and vulnerabilities could be searched independently, but their records were interlinked, allowing developers to move between artifacts without losing context.
From the moment a user lands, search unifies discovery, validation, and navigation across artifact types. The product architecture was organized around three core developer jobs: search quickly, choose confidently, and remediate effectively.
Guide was structured to support immediate orientation, whether a user arrived with a known component identifier or an exploratory query.
Global search unified components, vulnerabilities, and documentation within a single entry point. Predictive matches, direct routing for exact identifiers, and categorized results allowed developers to validate or investigate without switching contexts.
Browsing and default ranking logic were designed to support risk evaluation prior to integration decisions.
Components surfaced only their latest versions by default, reducing noise and emphasizing current state. Results were sorted by Trust Score, while vulnerabilities defaulted to most recent disclosures. These defaults encouraged safer evaluation patterns without removing user agency.
Guide organized component and vulnerability records as interconnected nodes within a larger decision-making ecosystem.
Each record surfaced Trust Score, compliance status, and severity alongside navigable dependencies, dependents, and version relationships. Users could move across related artifacts without losing orientation, allowing them to assess not just a single record, but its broader impact.
Developed as a first-class metric, Trust Score aims to provide immediate risk context at the component version level. A numerical value (0-100), paired with a color signal and iconography, communicates sentiment at a glance.
Trust Scores appear on all component detail pages, within search results, and while browsing.
Policy compliance was simplified at the browsing level to a binary pass or fail state, represented by a green check or red X. On detail pages, compliance expanded into explicit criteria including malware detection, CVSS threshold, and copyleft licensing.
A dedicated Policy page in the UI further explains compliance criteria and related visual indicators.
Record pages were organized into structured tabs that preserved orientation while enabling lateral movement. Users could navigate between versions, dependencies, dependents, and vulnerabilities without resetting search context or losing their place.
This pattern reduced reliance on back navigation, supported deep analysis, and reinforced relational continuity.
Search behavior adapted to user intent. Exact component identifiers and vulnerability IDs routed directly to their respective records, while broader queries surfaced categorized results with tab-level counts and filtering.
Predictive dropdown results while input text is typed accelerated validation without forcing mode changes.
Guide supported logged-out, free, and paid user states, prioritizing usability and usefulness across the board.
Proprietary intelligence (Trust Score, recommendations, insights) was visually gated through blur states, contextual tooltips, and sign-up prompts encouraging anonymous users to register for free.
Free users received a limited monthly credit allotment with persistent usage indicators and proactive notifications. Paid tiers received higher allowances.
A dedicated Usage page surfaced current status and historical trends, positioning credit tracking as visible infrastructure rather than hidden constraint.
Guide was developed during a period of significant organizational transition, with role eliminations scheduled to take effect on the product's December release date. Within days of receiving notice, I was selected to lead design for a new executive initiative and ship a net-new product under that same deadline.
With no existing product foundation, alignment across leadership, product, and engineering became essential. I partnered closely with the Director of Design and the Chief Product Development Officer to define scope, navigate tradeoffs, and reconcile requirements against constraints. The UX Lab served as a shared, production-aligned environment where workflows could be evaluated against real data rather than debated abstractly.
Engineering collaboration was continuous. Interaction patterns and information models were reviewed directly within the UX Lab, surfacing feasibility considerations early and shaping implementation sequencing around actual user journeys.
Product Marketing progressed in parallel. Naming, visual direction, and launch positioning were developed before the product formally existed. The UX Lab provided a functional, data-rich reference that informed landing page development and messaging alignment.
Research inputs were synthesized from existing workshops, design sprints, and user interviews. Targeted usability sessions validated search behavior, signal clarity, and monetization touchpoints prior to release.
Guide shipped on schedule following sustained cross-functional iteration and executive visibility throughout development.
Guide launched on its scheduled release date as a fully functional security intelligence platform, establishing a new entry point into Sonatype's ecosystem.
Internal reception was strong across product, engineering, and executive leadership, with Trust Score and policy transparency resonating as a clear, differentiated evaluation model.
Existing enterprise customers responded positively during early demos, and several major organizations committed to subscriptions prior to general availability.
Adoption of the UX Lab changed implementation dynamics by grounding workflow sequencing and feasibility discussions in production-aligned behavior rather than static documentation.
Guide clarified that enterprise usability is less about simplification and more about sequencing. Developers do not need fewer signals; they need signals presented at the right moment and in the right order.
By restructuring evaluation around orientation, confidence, and impact, the product shifted security from a downstream interruption to an upstream decision surface. Defaults, ranking logic, and visible relationships shaped behavior in ways that documentation alone could not.
Designing directly in code strengthened cross-functional alignment. When interaction models are inspectable and grounded in real data, conversations center on implementation and tradeoffs instead of interpretation. Shared artifacts reduce friction, particularly under compressed timelines and executive visibility.
The project also reinforced the importance of durable platform architecture. Individual developers and enterprise teams rely on the same intelligence, even as their needs differ in depth and scale. Systems designed with flexibility at their core can expand without structural rework.